What is even OSINT? OSINT at its core stands for open-source intelligence and Wikipedia defines it as follows:
Open-source intelligence (OSINT) is the collection and analysis of data gathered from open sources (overt and publicly available sources) to produce actionable intelligence.
OSINT is used by various entities to gain information or insights on specific topics. Insurance companies, for example, use OSINT to assess the risk of their insurance policies. Other areas where OSINT is used on a daily basis include the military, intelligence agencies, law enforcement, banks and, of course, cyber criminals.
Those criminals use OSINT to obtain as much information as possible about a potential target. While the target may be a company or an individual, the type of information that is relevant differs significantly. In the case of an individual person, for example, the following information could be relevant to an attacker:
- Birth date
- Pet’s name, mothers maiden name, first car, etc. (useful for security questions)
- Current and past addresses
- Credit card or other payment information
- Phone number and email address
- Other useful information about the persons life
A company, on the other hand, usually offers a larger attack surface than an individual, which is why other factors are also of interest to an attacker. A major issue here is the exposed technical attack surface of a company, which can consist of domains, subdomains, servers, web applications and services, among other things.
We would like to use an example to illustrate how an attacker can use OSINT to attack a company.
Companies as a target for OSINT
In this example an attacker targets “Example Corp LLC” in order to extort money with ransomware.
First, they might try to find information about the employees to gain initial access via phishing. Since a company usually consists of several individuals, the points already mentioned in the introduction are also relevant in the case of an attack on a company.
In our example, the attacker can search for employees and their corresponding role in the company on LinkedIn. Usually, not much more information is needed to perform a phishing attack, as the corresponding email addresses can be found in various databases. If the phishing email is well crafted and the company lacks other security measures to prevent this type of attack, preferably with a defense-in-depth approach, such an attack is likely to succeed.
However, since the attacker in our example also wants to try another attack angle, they will use OSINT to enumerate the external technical attack surface.
They already know that one of the companies domains is example.com, as this is the main site of the targeted company. By using OSINT techniques they find two more domains that are associated with Example Corp LLC or their recent acquisition “Illustration LLC”. This leads to the following three root domains which can be enumerate even further:
example.comexample.co.ukillustrationllc.com
The next step is to try to find the subdomains of these three domains by using bruteforce or other means. Our attacker might find dozens, hundreds or thousands of subdomains, depending on the size of the company and their infrastructure.
Not all subdomains point to an actual server, but the attacker can easily sort out those false positives which results in the following:
www.example.comabout.example.com- …
www.illustrationllc.comdev.illustrationllc.comtest.dev.illustrationllc.com
They might filter the subdomains further to look for interesting features such as unusual open ports, web servers with login pages, directory listings, outdated software, and so on. They might even find a few exposed FTP ports on some older infrastructure.
In our case one of those filtered subdomains stands out: test.dev.illustrationllc.com. On this domain a CMS software with a login page can be found:
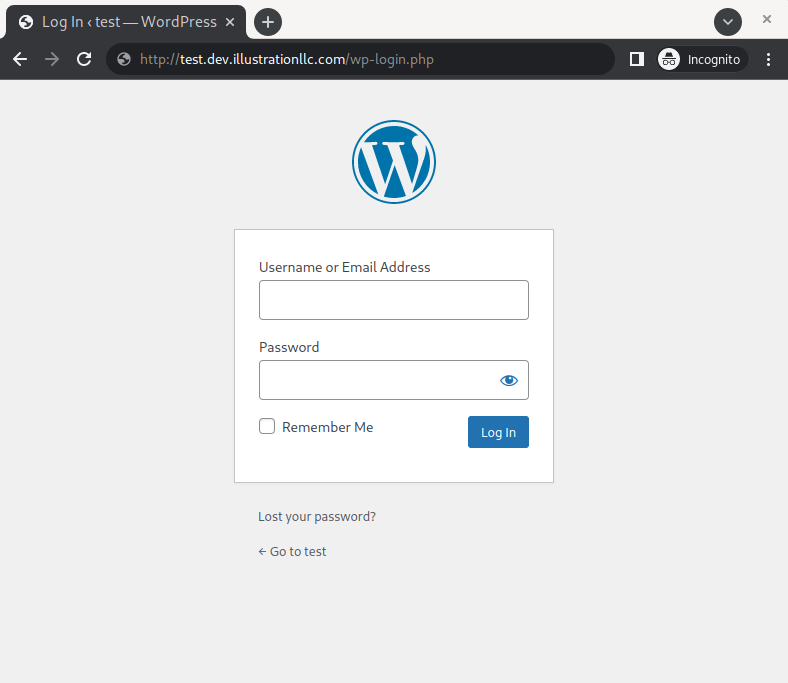
Sample login page of a Wordpress installation.
After further enumeration of the webserver, our attacker finds out that this is a version that is outdated and even contains publicly available vulnerabilities. Apparently this web server was set up here years ago and has since been forgotten.
Good for our attacker, but bad for the company. The attacker manages to gain access to the underlying host thanks to the many security holes. Since this server was also set up at a time when the company only used its on-premise server, the attacker is now also in the internal network. An ideal place to start the ransomware attack.
This is just one example of the plethora of ways an attacker can use OSINT to gain access to an organization’s network.
Conclusion
As we have seen in this example, it is essential for a company to reduce its own attack surface. But to do this, one must first get to know and understand their own attack surface. This is where we come into play with our OSINT analysis, in which we take a close look at your company through the eyes of an attacker.
After you have an overview of your company’s attack surface, you can start planning the next steps to reduce exactly that surface. With an initial risk assessment of each asset from our side, you can also prioritize your assets for deeper evaluation.
This could be a pen test, a code review or just shutting down the found legacy applications and servers.
